Top military health officials recently highlighted the importance of maintaining premium care for patients at a time when information technology systems are changing rapidly across the Military Health System.
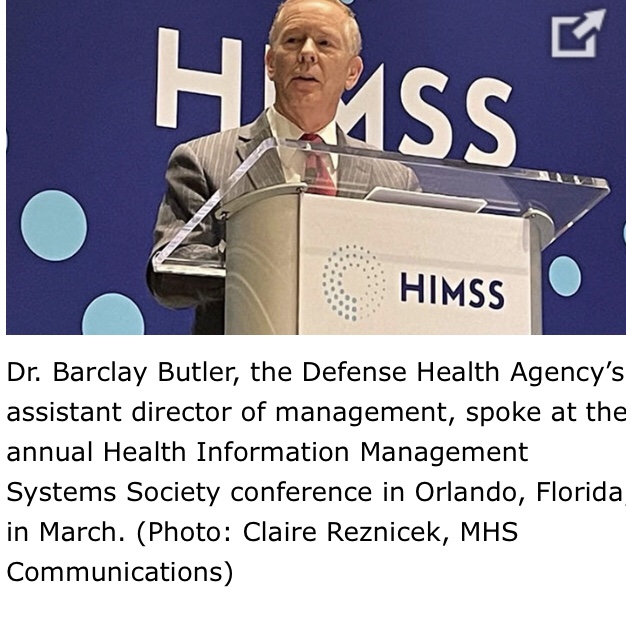
Speaking at the Health Information Management Systems Society conference in Orlando, Florida, in March, Dr. Barclay Butler, the Defense Health Agency’s assistant director of management, spoke about the intricacies of institutional transformation, especially standardization and consolidation.
“This transformation changes everything,” Butler said. “Everything except the care of our patients.”
Butler said the DHA is placing a high priority on protecting staff from burnout while focusing on their goals and patient care.
Following Dr. Butler’s presentation was a briefing from Lance Scott, the program manager for the Defense Medical Information Exchange program, and Crystal Baum, the Joint Health Information Exchange product owner for the Federal Electronic Health Record Modernization Office.
They talked about optimizing and expanding the joint health information exchange. They highlighted specific programs underway such as the effort to use natural language processing to make searching easier for providers. They also talked about the retirement of older software systems and what that really looks like in practice.
The conference’s second day featured a panel discussion on “Experiencing, Enhancing, and Evolving Federal Electronic Health Records.” Experts talked about how systems like MHS GENESIS foster innovation and improve responsiveness.
Pat Flanders, DHA’s chief information officer and the deputy assistant director for information operations, said that often there are the “haves and the have-nots when it comes to [Military Treatment Facilities], and the smaller MTFs wonder why they don’t have access to the same systems and opportunities. A standardized electronic health record bridges that gap.”
Meanwhile, Holly Joers, program executive officer for Defense Healthcare Management Systems, said deploying the standardized electronic health records is a team effort. “Our success as a team relies on doing this with commanders on the ground,” she said. “Not to them or for them. But with them.”
Flanders recalled his own military retirement as a difficult process involving a three-month search to locate his health records. In the future, however, Flanders said he hopes others will be able to complete that same process by just checking a box on the computer.
The conference’s second day concluded with Army Lt. Gen. Ron Place, the DHA’s director, providing keynote remarks and a briefing entitled, “Clear and Present Danger.” Place began by noting that human beings aren’t perfect, but technology can be a solution to reduce human error. “Done right, health IT can make doing the right thing the easy thing,” said Place.
The director closed his remarks by reminding the audience that the single most important factor that determines whether an injured or wounded service member survives isn’t the talented combat surgeon or doctor back home, but “the skills of the medics and corpsmen who treat the fallen soldier, sailor, airman, or Marine on the battlefield [where] technology, communication and rapid evacuation may not be available.”
Place emphasized that although “we utilize technology to train our medical teams and to outfit our home stations, deployed hospitals and clinics … our most important tool is the medic or the corpsman stepping out into the unknown, unafraid, with the skills gained through training and experience – the sets and reps needed to hone those skills.
The final day of DHA engagement at the HIMSS conference closed with motivational words from Dr. Brian Lein, the DHA’s assistant director for healthcare administration.
Lein provided a frank and illuminating brief on “Developing the Military Medical Digital Patient Experience.” He issued a stark reminder for all those working within the MHS. “There’s no other healthcare system in the world that has our mission. We have to focus on readiness first,” Lein said.
While discussing the future of digital health care in the era of COVID-19 and the use of electronic health records, he declared “we cannot optimize until we standardize.”
Article link: https://health.mil/News/Articles/2022/04/05/How-Health-IT-Upgrades-are-Transforming-the-Military-Health-System