As the U.S. Air Force continues its aggressive pursuit of modernization and prepares for the future fight, the head of the service wants to put words into action and get meaningful military capabilities into the hands of warfighters faster than ever before.
“I’m not very interested in experimentations or demos. I’m prepared to accept risk and move towards fielding with engineering and system development programs that lead to production and lead to production at scale,” Air Force Secretary Frank Kendalltold an audience at the Potomac Officers Club’s 2022 Air Force Summit in Tysons, VA.
“If the risk appears to be manageable and we have reasonable mitigations, we need to get on with it and get towards production,” said Kendall, a Wash100 Award recipient. “The result of that inevitably would be some cost and schedule hiccups as we go forward, but I’m afraid we’re going to have to pay that price to get to where we need to go.”
This urgency stems in part from what Kendall has seen as a decline in the Air Force’s dominance since the Cold War. Speaking from his breadth of experience in government, military and industry, Kendall acknowledged that the Air Force’s analytical, science and engineering capabilities have atrophied in the past few decades. Now, as the head of the Air Force, Kendall hopes to reestablish that dominance.
Kendall was sworn in as Air Force secretary in July 2021, and in his remarks during the event, he reflected on the strides the service has made — as well as the ways in which the threat landscape has changed — throughout his first year in the role.
“I came into office with two fundamental roles. One was to put us in a better position relative to our principal competitor, and that is of course, China,” Kendall reiterated.
Priority Number One: China
China’s military modernization program is something Kendall has expressed deep concern about since his return to the public sector in 2010, when he took on the role of principal deputy under secretary and acting under secretary of defense for acquisition, technology and logistics at the Department of Defense.
At that time, Kendall said he could already see that China was on a path to field systems that were intended to defeat the United States’ ability to project power. “We had to respond to that,” he remembered. In the 12 years since that point, however, the systems that China had in development have been fielded, and now the country is working on even newer systems.
“So this is an ongoing quest for technological military superiority that we have got to move quickly in, but we also have to make the right choices about what we invest in,” Kendall said.
Looking at the risk profile the U.S. faces today, Kendall noted that it will not lessen over time. Instead, the nation’s adversaries will be looking ahead to our capabilities in the pipeline for the future and building systems to defeat them.
“We have got to be thinking ahead of that and moving ahead of that. That risk is going to go up over time, and you’re seeing increasing aggressive behaviors on the part of China,” he warned.
Priority Number Two: Reestablishing Air Force’s Operational Power
The second objective Kendall had coming into the Air Force was to leave the Air Force better than he found it. This objective, he admitted, “covers an enormously wide swath of things” including, importantly, strengthening the institution’s technological capability.
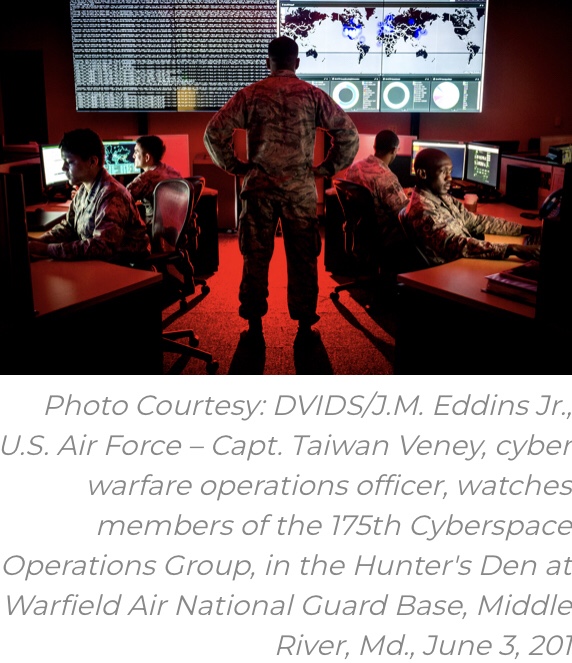
Kendall’s second objective also led to the creation of his seven Operational Imperatives — an effort which he describes as a “list of seven things that I felt that we had to do better at to be successful operationally in conventional power projection.”
These imperatives cover top programs and mission areas including space, the Advanced Battle Management System, Next Generation Air Dominance and Air Force readiness in the future battlespace. In the seven months since Kendall revealed his Operational Imperatives, he has put together teams — led by operators, technologists and acquisition executives — to see the imperatives to fruition.
Reflecting on this progress, Kendall said, “The teams have done great work at pulling together what we need to do. The problem now, for me, is to resource it.”
Budget
Fortunately, Kendall expects the Air Force’s top priority programs to be well-funded. “Congress is likely to provide a significant increase in [2023] from what we asked for. This would reset our baseline for [2024],” he projected.
The Air Force’s most recent Program Objective Memorandum, or POM, is just a starting point for the budget and funding conversations Kendall expects to have in the next few months. However, until budgets are finalized, the Air Force won’t know for sure which resources will be allocated to which programs.
“We don’t really know where we’re going to end up in terms of resources, but I think we’ve positioned the Department of the Air Force very well to compete for those resources, because we have identified the specific things that we need to do.”
Though Kendall could not share details about the latest POM, he did say, “I will tell you that I made tradeoffs in the POM to fund as much of the Operational Imperatives as I could.”
DOD-Wide Cultural Shifts Necessary
Ultimately, Kendall acknowledged that the Air Force won’t overcome the myriad of threats it faces if the Department of Defense doesn’t integrate and operate as a cohesive joint force.
“There’s an enormous amount of parochialism, turfism, etc. that I have seen in the Department of Defense, and we’ve got to get beyond that,” Kendall urged. “We’ve got to think about what our mission is and how we contribute to that mission and make sure that what we’re doing contributes as much as possible and not spend our time just trying to take care of our little part of the budget.”
“One team, one fight” is a mantra that guides Kendall in his role as he hopes to drive out the “dysfunctional” behavior in the Pentagon and enact the same mentality across the entire DOD enterprise.
The 2022 Air Force Summit is part of the Potomac Officers Club’s annual military service-focused program of events. The next installment of the series will be the 2022 7th Annual Army Summit on Aug. 24 at the McLean Hilton.
Hon. Gabe Camarillo, undersecretary of the Army and chief management officer for the U.S. Department of the Army, is slated to keynote this highly-anticipated in-person event. Click here to register.
Article link: https://www.govconwire.com/2022/07/air-force-secretary-frank-kendall-prepared-to-accept-risk-to-field-capabilities/