Dan Goodin 05/6/2022 2:33 pm

For more than a decade, we’ve been promised that a world without passwords is just around the corner, and yet year after year, this security nirvana proves out of reach. Now, for the first time, a workable form of passwordless authentication is about to become available to the masses in the form of a standard adopted by Apple, Google, and Microsoft that allows for cross-platform and cross-service passkeys.
Password-killing schemes pushed in the past suffered from a host of problems. A key shortcoming was the lack of a viable recovery mechanism when someone lost control of phone numbers or physical tokens and phones tied to an account. Another limitation was that most solutions ultimately failed to be, in fact, truly passwordless. Instead, they gave users options to log in with a face scan or fingerprint, but these systems ultimately fell back on a password, and that meant that phishing, password reuse, and forgotten passcodes—all the reasons we hated passwords to begin with—didn’t go away.
A new approach
What’s different this time is that Apple, Google, and Microsoft all seem to be on board with the same well-defined solution. Not only that, but the solution is easier than ever for users, and it’s less costly for big services like Github and Facebook to roll out. It has also been painstakingly devised and peer-reviewed by experts in authentication and security.

The current multifactor authentication (MFA) methods have made important strides over the past five years. Google, for instance, allows me to download an iOS or Android app that I use as a second factor when logging in to my Google account from a new device. Based on CTAP—short for client to authenticator protocol—this system uses Bluetooth to ensure that the phone is in proximity to the new device and that the new device is, in fact, connected to Google and not a site masquerading as Google. That means it’s unphishable. The standard ensures that the cryptographic secret stored on the phone can’t be extracted.
Google also provides an Advanced Protection Program that requires physical keys in the form of standalone dongles or end-user phones to authenticate logins from new devices.
The big limitation right now is that MFA and passwordless authentication get rolled out differently—if at all—by each service provider. Some providers, like most banks and financial services, still send one-time passwords through SMS or email. Recognizing that those aren’t secure means for transporting security-sensitive secrets, many services have moved on to a method known as TOTP—short for time-based one-time password—to allow the addition of a second factor, which effectively augments the password with the “something I have” factor.
Physical security keys, TOTPs, and to a lesser extent two-factor authentication through SMS and email represent an important step forward, but there remain three key limitations. First, TOTPs generated through authenticator apps and sent by text or email are phishable, the same way regular passwords are. Second, each service has its own closed MFA platform. That means that even when using unphishable forms of MFA—such as standalone physical keys or phone-based keys—a user needs a separate key for Google, Microsoft, and every other Internet property. To make matters worse, each OS platform has differing mechanisms for implementing MFA.
These problems give way to a third one: the sheer unusability for most end users and the nontrivial cost and complexity each service faces when trying to offer MFA.
Taming the MFA beast
The program that Apple, Google, and Microsoft are rolling out will finally organize the current disarray of MFA services in some significant ways. Once it’s fully implemented, I’ll be able to use my iPhone to store a single token that will authenticate me on any of those three companies’ services (and, one expects, many more follow-on services). The same credential can also be stored on a device running Android or Windows.
By presenting a facial scan or fingerprint to the device, I’ll be able to log in without having to type a password, which is faster and much more convenient. Equally important, the credential can be stored online so that it’s available when I replace or lose my current phone, solving another problem that has plagued some MFA users—the risk of being locked out of accounts when phones are lost or stolen. The recovery processes works by using an already authenticated device to download the credential, with no password required.
“That’s really the whole point here—there’s no recovery process as the private key is immediately available across a user’s devices,” Andrew Shikiar, executive director of the FIDO Alliance, wrote in an email. “They just need to verify themselves to their device to log into their previously enrolled accounts.”
He added: “If the question is about device cloud recovery (e.g., how do I get back into my iCloud account?)—that is something that is managed by each platform provider, all of whom have highly secure methods to ensure that recovery is possible for authentic users.”
Besides giving end users a much more usable process for logging in, the program also offers robust security protections that go beyond what’s available from most online services today.
“While any MFA is better than no MFA, only FIDO authentication is phishing-resistant and is the MFA gold standard,” Bob Lord, a senior technical advisor in the Cybersecurity Division at the Cybersecurity and Infrastructure Security Agency, told me. Previously, Lord was the chief security officer for the Democratic National Committee and chief information security officer at Yahoo. “We finally have a cryptographically strong MFA that is based on open standards and is built into the browsers and phones we already use. That drives costs down and reduces complexity for organizations that want to remove credential theft from the attacker’s toolkit.”
The linchpin to this scheme is something called “multi-device credentials” or, more colloquially, “passkeys,” introduced in updates to the existing FIDO, WebAuthn, and CTAP standards for authentication. As the name suggests, the credential works across all devices, whether you’re running iOS, Android, or Windows, and across all Apple, Google, or Microsoft services.
To make passkey authentications immune to phishing and other common forms of credential theft, the phone or other device storing the credential must be in proximity to the device the user is using to log in. A Bluetooth connection allows the two devices to exchange information that ensures the device logging in is near the end user rather than a remote threat actor. It also allows the authenticating device to ensure that the machine logging in is connected to the legitimate URL rather than an imposter attempting to gain unauthorized access.

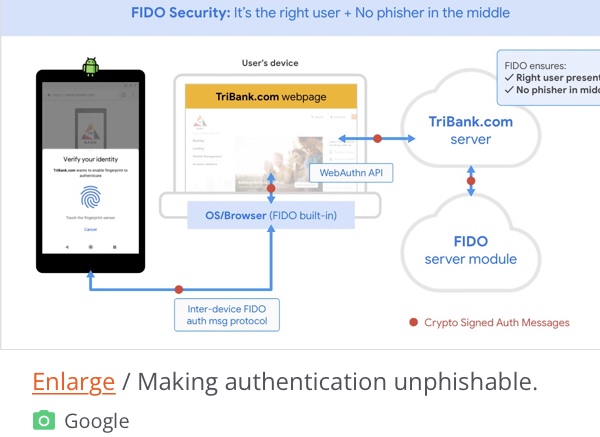
So even if a remote attacker attempts to log in, account owners will be unable to use their passkeys to authenticate the transaction. Since the phone or other authenticating device must be physically close to a user’s computer before it will display a “do you want to login” dialog, a phisher in another city, state, or country can’t initiate a login and perform a technique known as MFA prompt bombing.
Lord and other security experts say that passkeys also eliminate the need to enter a password without degrading security assurances provided by most current forms of MFA. Most MFA has consisted of a password and a security token—that is, something I know and something I have. The new system provides another, easier form of MFA—specifically, something I have (my phone) and something I am (my fingerprint or face scan).
In an email, Andrew Shikiar, executive director of the FIDO Alliance, said that he expects rollouts to start by the end of this year and early into the next year.
“Each platform provider has their own timelines for initial deployment over the coming year,” he wrote. Once all three services have fully implemented the system, “users will be able to leverage the ‘passkey’ functionality for passwordless logins across devices on a device platform and also can bootstrap from one platform to another that also has support. This latter action is done via a local Bluetooth pairing in a new protocol being built into the FIDO specs.”
The FIDO Alliance, Google, and Microsoft have more details here, here, and here.
Given the decade of empty promises announcing the demise of the password, people have good reason to greet this week’s announcement with skepticism. It won’t be a done deal until all the pieces are in place and passkeys are rolled out on a mass scale. That said, with the support of Google, Microsoft, and especially Apple—a company famous for its “not invented here” bias—we’re for the first time within spitting distance of this key landmark.
Article link: https://arstechnica.com/information-technology/2022/05/how-apple-google-and-microsoft-will-kill-passwords-and-phishing-in-1-stroke/?
This post has been updated to add comment from FIDO explaining how the recovery process works.